IoT Security
Protect your Business with Next-Gen Iot Security as a Service
We offer a next-generation Red Team program that offers a cost-effective security testing program that will be a pioneer in your road map. We implement and manage the IoT security testing program management office for customers to achieve the optimal performance
The client management office ensures quality deliverables and creates an exclusive communication channel to build a cyber-resilient customer organization
PLATFORM SERVICES
Our PENTEST365 platform is integrated with client organization security suites to identify the security issues
SOLUTION & CONSULTING
Our expert assessments and recommendations will offer cutting-edge solutions to secure customer data
PROGRAM MANAGEMENT
We Build robust cost-effective programs and operate with greater efficiency and Transfer seamlessly

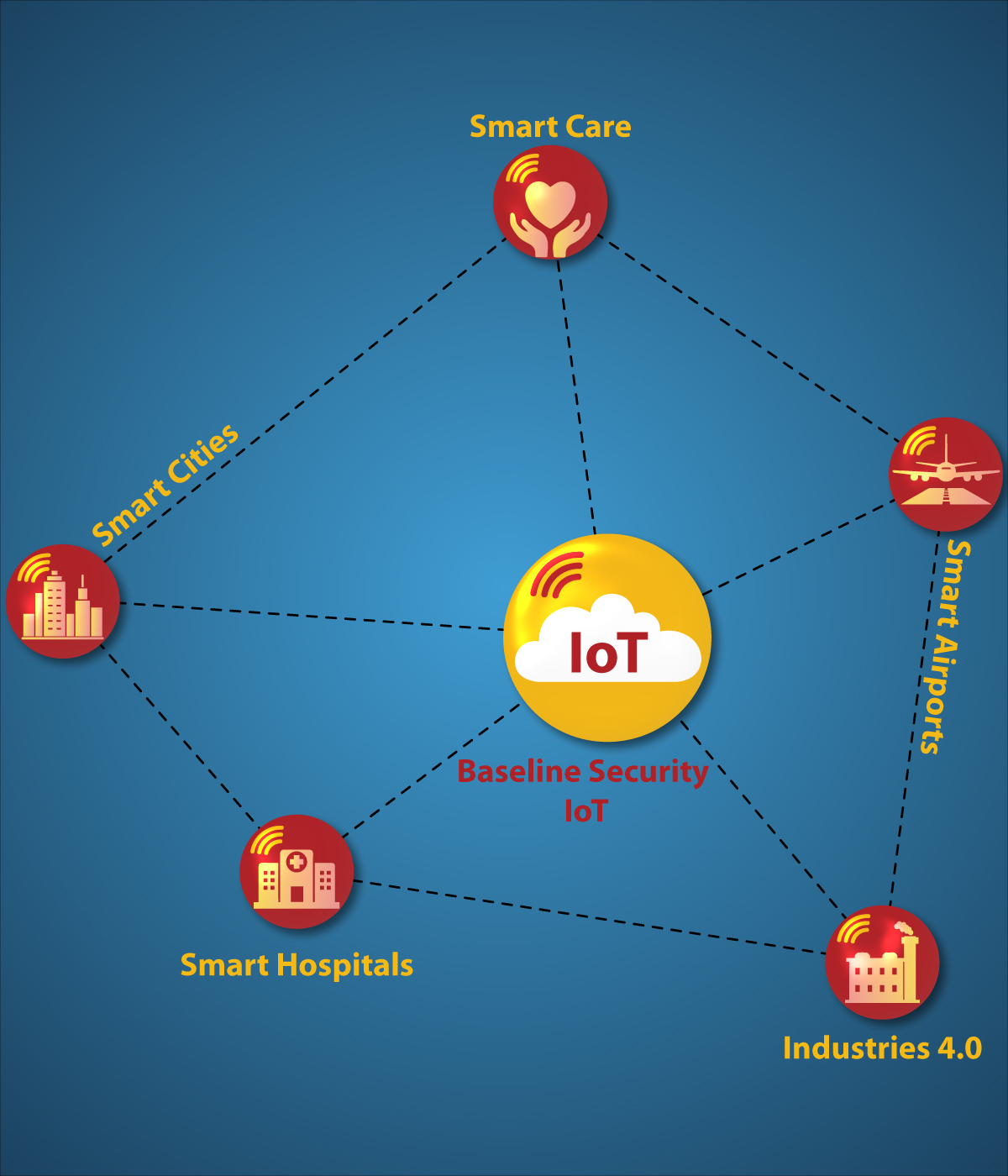
Security threats are an increasing trend in the industry and attackers have no mercy whether it is small or bigger organizations. Internet of Things (IoT) influence is home to bigger industries and the deeper connectivity of many devices that are truly helpful but most of the products are designed without security baselines. Our IOT Red team addresses the potential gaps in identifying the threats, analyzes all possible assets, and cross maps with cyber threat intelligence to design a real-world adversary attack plan.
A unique Cyber Attack Kill Chain methodology that involved various phases and activities coverage ranging from System builds, web and API interfaces, network protocols, and wireless & Bluetooth communication channels. The entire attack emulation will be performed by an external attacker who does not know the internet-facing applications or the underlying infrastructure with the goal being to compromise the internal network and gain a foothold on the network. We will engage the appropriate subject matters experts from a partner organization to crack down on the attacking emulation scenarios.
Our comprehensive report will be limited to real fixes. The detailed report contains the type of attack performed, the attack path, vulnerable points and screenshots.
Start Your Trail TodayOUR SERVICES
Bug Bounty
Bug bounty programs help organizations to identify potential vulnerabilities on critical assets at a faster pace
READ MORE +Red Teaming
Perform a comprehensive adversary simulation to measure your company cyber security posture
READ MORE +DevSecOps
DevSecOps as a Service will help you automate the implementation of threat modeling to identify potential threat vectors and attack
READ MORE +IoT Security
9IoT security is the practice that keeps your IoT systems safe. IoT security tools protect from threats and breaches, identify and monitor risks and can help fix vulnerabilities. IoT security ensures the availability, integrity, and confidentiality of your IoT solution.
READ MORE +Threat And Vulnerability Management
Vulnerability management services provide critical visibility across all your IT assets .where they are most vulnerable. From there, our team will prioritize remediation tactics to further improve your security posture
READ MORE +Cloud Security Assessment
Identify potential weakness which can be exploited to perform attacks such as sensitive data exposure
READ MORE +Audit & Accreditation
CyberOne is an independent audit & accreditation firm helping customers to plan, develop, and implement compliance & certification programs and we will conduct independent & certification audits.
READ MORE +Vulnerability Disclosure Program
With increasing technologies and platforms, the rise of cyber-attacks has become threefold. It is important to maintain proper cyber hygiene to avoid attacks on the organization’s assets.
READ MORE +LET'S TALK ABOUT YOUR CYBER NEEDS
CyberOne SME's will protect your environment from Advisories